
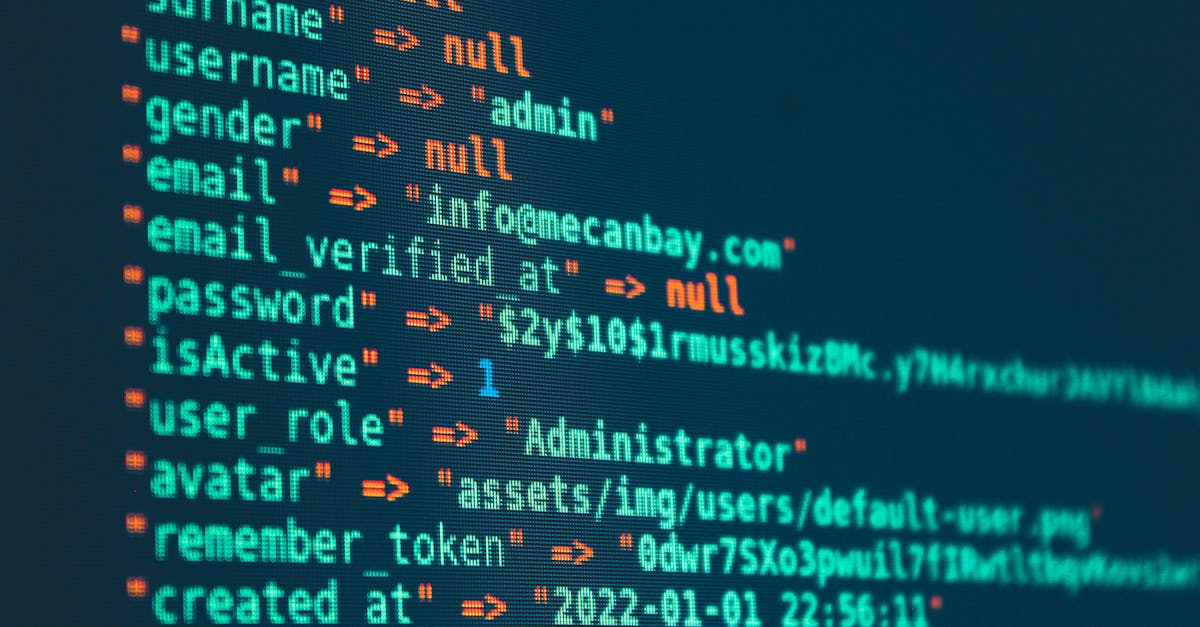
How to verify AI-discovered vulnerabilities aren't just training data echoes
AI security tools sometimes 'discover' vulnerabilities they actually memorized from training data. Here's a practical workflow to tell the difference.

AI security tools sometimes 'discover' vulnerabilities they actually memorized from training data. Here's a practical workflow to tell the difference.

When auth providers add phone or QR verification to signup, automated account creation breaks. Here's how to redesign your pipelines to never depend on it.

Docker publishes ports by editing iptables directly, which skips UFW entirely. Here's why it happens and three ways to actually lock things down.

A grounded look at TokenSpeed, the new LLM inference engine trending on GitHub, plus a practical benchmark you can actually run yourself.
A practical guide to debugging surprise cloud bills, tracing NAT gateway traffic with VPC Flow Logs, and setting up guardrails to prevent recurrence.

Your Docker containers take 10 seconds to stop? It's almost always the PID 1 signal-handling problem. Here's the root cause and the fix.

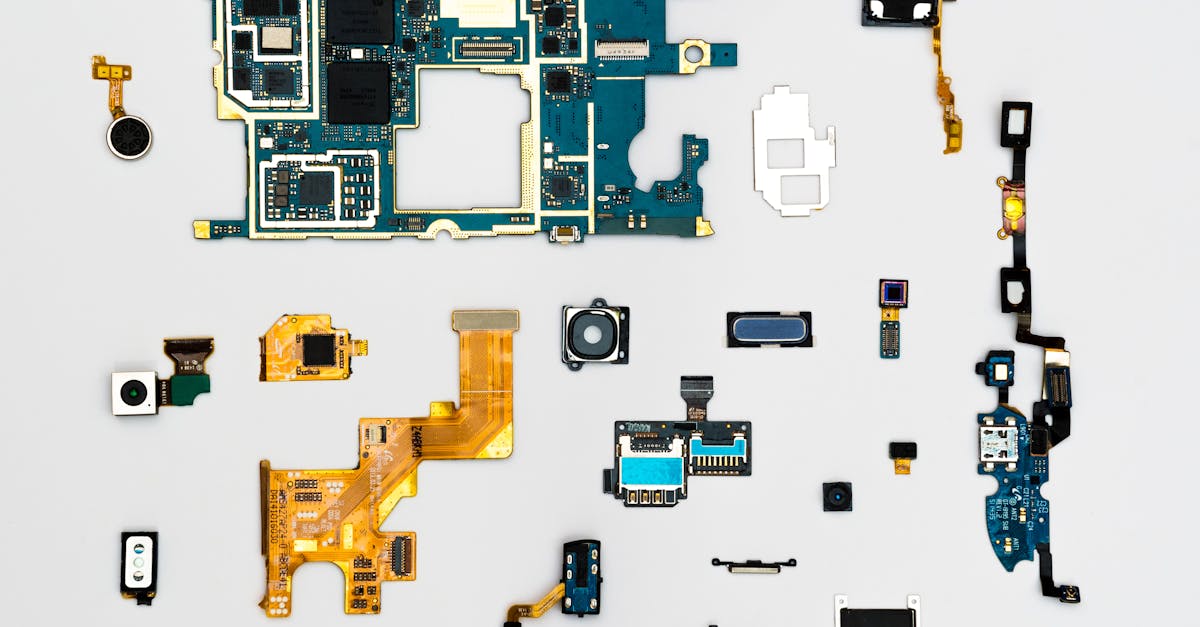
Comparing three approaches to giving AI agents filesystem access — raw allowlists, container isolation, and virtual FS layers like Mirage.

Binary AI disclosure flags collapse a spectrum into one bit and end up incentivizing dishonesty. Here's how to design provenance that actually works.

A step-by-step guide to diagnosing and fixing common Barman backup failures for PostgreSQL, from SSH issues to WAL archiving and replication slots.

Most teams have zero visibility into their AI workload's water and energy footprint. Here's how to measure it, optimize it, and report it clearly.

Learn how to diagnose and fix regional IP blocking that takes down legitimate cloud-hosted apps as collateral damage from bulk anti-piracy enforcement.

How to set up a self-hosted Discourse forum for digital sovereignty — from server provisioning to backups and maintenance.

Step-by-step guide to solving GPU memory issues when self-hosting Mistral Medium 3.5 128B with vLLM, tensor parallelism, and smart configuration.

Government open-source repos are hard to reuse. Here's how to structure institutional code with publiccode.yml, externalized config, and proper dev setup.

A practical guide to migrating open-source projects away from GitHub — covering git history, issues, CI pipelines, and how to keep contributors along the way.

pgbackrest is reportedly no longer maintained. Here's how to audit your PostgreSQL backup setup and migrate to alternatives like Barman or WAL-G.

How to secure voice and biometric training data in ML pipelines — encryption, scoped access, audit logging, and data minimization techniques.

Learn how to audit, monitor, and optimize your AI coding tool costs as the industry shifts to usage-based billing. Practical scripts and strategies included.

AI coding assistants are shifting to usage-based billing. Learn how to track, optimize, and control your AI tool costs before they spiral out of control.

AI agents with unchecked database access are a disaster waiting to happen. Here's how to sandbox credentials, restrict permissions, and prevent autonomous tools from destroying production data.

Learn how to protect your domains from unauthorized transfers with transfer locks, registry locks, DNSSEC, and proactive monitoring scripts.
Binary config files break across versions and block code review. Here's how to audit, convert, and enforce plain text formats for resilient projects.

Debug and fix common LLM API integration issues: token mismanagement, output quality degradation, and lack of observability in production.

Understanding why HTTPS traffic gets blocked by DPI, how domain fronting and HTTP tunneling work, and practical solutions for restrictive networks.

Fix the frustrating Linux laptop battery drain during suspend. Learn why s2idle vs S3 sleep matters and how to debug and solve it.

A step-by-step playbook for rotating secrets, auditing access, and hardening your setup after a deployment platform security breach.

A step-by-step incident response playbook for developers when their deployment platform reports a security breach. Covers secret rotation, access auditing, and hardening.

When your domain lands on a DNS blocklist, your entire lab breaks. Here's how to diagnose, fix, and prevent DNS blocklist issues.

Learn how copy-on-write database branching solves the pain of testing Postgres schema migrations, with practical workflows and CI/CD integration.

How to migrate from shared hosting to a VPS — a step-by-step guide covering server setup, data migration, Nginx config, and the performance gains you can expect.

A step-by-step guide to migrating your production infrastructure between cloud providers without downtime or data loss.

AI agent orchestration code becomes unmanageable fast. Here's why general-purpose languages struggle with AI workflows and how DSL-based approaches solve it.

Fix your team's scattered knowledge problem by self-hosting a forum. Step-by-step guide covering Discourse, Flarum, and NodeBB setup.

Step-by-step guide to migrating from cloud object storage to self-hosted MinIO, covering setup, data migration, and operational trade-offs.

AI agents sending email often land in spam. Here's how to fix SPF, DKIM, and DMARC issues and build reliable programmatic email delivery.

Most engineering teams have no idea what their work actually costs. Here's a practical framework for tracking effort allocation and making better decisions.

When AWS Lambda costs and cold starts become unsustainable, here's how to evaluate containers as an alternative and migrate incrementally.

Why Python scripts fail in self-hosted n8n Docker containers and how to fix it with custom images, virtual environments, and sidecar patterns.

How to audit your cloud region dependencies and build multi-region resilience before data center capacity constraints break your infrastructure.

A step-by-step guide to self-hosting your own email server with Mailcow, DNS configuration, deliverability debugging, and maintenance tips.

Learn how to evaluate AI model safety before production deployment using system cards, safety probes, and continuous monitoring.

Your app relies on hundreds of open-source packages nobody has reviewed. Here's how to audit, scan, and lock down your dependency chain before it bites you.

How to debug and prevent silent API failures when integrating with platforms that have multiple services sharing confusing, overlapping names.

Your HTTPS traffic gets decrypted at reverse proxies before reaching your server. Here's how to audit, fix, and prevent TLS termination blind spots.

Accidentally committed secrets to git? Deleting the file isn't enough. Here's how to actually purge sensitive data from your entire git history.

Intermittent CI pipeline failures aren't random. Learn how to diagnose and fix the three most common causes: race conditions, resource exhaustion, and flaky dependencies.

SSH key management breaks down at scale. Learn how SSH certificates eliminate authorized_keys sprawl, automate offboarding, and fix host verification.

WordPress plugins run with zero sandboxing. Here's how to contain the damage with containerization, network rules, and least-privilege database access.

Step-by-step guide to diagnosing and recovering from Git repository corruption, from broken HEAD refs to damaged packfiles.

Fix the most common reasons self-hosted production apps crash overnight — memory limits, disk issues, health checks, and the operational basics most guides skip.

Step-by-step guide to bypassing Windows 11's mandatory Microsoft account during setup, with methods for VMs, clean installs, and automated deployments.
Fix broken builds from dependency rot when revisiting old projects. Step-by-step debugging guide for stale Node.js and Python dependencies.

AI agent tool integrations often ship with wide-open permissions and zero input validation. Here's how to lock them down before someone else finds out.

How to detect, recover from, and prevent container scanner supply chain attacks after Trivy's vulnerability database was compromised.

Learn how to debug and fix DNS resolution failures when security-filtered resolvers silently block legitimate domains you depend on.

TapMap now supports Linux and Docker. Here's how to set it up, where it fits in your stack, and what to watch out for.

Self-hosted email keeps getting rejected? Here's why IP reputation matters more than perfect DNS records, and how to maximize deliverability.

Fix the fragmented SSH debugging workflow on headless Linux servers by setting up Cockpit, a lightweight web-based management interface.